The World Wide Web as we know it is an insanely large collection of web pages that are found on the internet. A little confusing? I bet. Most people don’t realize that although used interchangeably, the internet and the world wide web, or web, are entirely different systems.
In essence, the internet is a massive network or labyrinth of networks of millions and millions of computers around the globe. While the internet provides the infrastructure, the world wide web is the collection of information that can be accessed on the internet. It is a system that we use to tap into the internet.
The internet or the web if you will is unimaginably huge. It is composed of an incredible number of web pages, databases, and serves. But the part of the web that we interact with every day through the use of search engines and web browsers is only the tip of the iceberg.
The Deep Web
Before we explore the dark web, it is pertinent we understand what the deep web is. When you type in queries into a search engine, you receive results with an index of websites that may contain what you are searching for. All of these results exist on what we refer to as the open or surface web.
Illustrating the web as an iceberg as we did earlier, the surface web is that protruding part of the iceberg you can see above the surface. Underneath this surface is a behemoth that contains web pages and content that cannot be accessed as part of your search results or with a traditional web browser.
The entirety of this portion of the world wide web is what is referred to as the deep web. There’s little spooky about the deep web. Basically, it contains content that is deliberately hidden from direct reaches such as medical records, financial and banking information, corporate records, government records and information, and academic databases.
The Deep Web is sometimes used interchangeably with the dark web but they are not the same concept. The deep web is largely benign and the information contained on it mostly belongs to enterprises, large corporations, and governments. It makes up over 90% of the entire web.
The deep web is hidden beneath the surface, but it does not take as complicated a process to access it as with the dark web. Dark web pages are usually hidden behind passwords, paywalls, and firewalls.
The Dark Web
Finally, we come to the deepest portion of that iceberg. The dark web is technically a subset of the deep web. A small subset. Dark web pages are very concealed and are more difficult to reach than those on the deep web. They are also not indexed by search engines and cannot be accessed by regular browsers.
The dark web has a notorious reputation, as I’m sure you may have gathered. This reputation is absolutely well earned. It is largely unregulated, and there is no system of control over it. As a result, it is the setting for a significant portion of the criminal transactions carried out over the internet.
A 2014 study by Dr. Gareth Owen of the University of Portsmouth discovered that the most commonly hosted content on the dark web is child pornography. On the dark web, one can buy guns illegally, hire assassins, buy credit card information, hacked streaming accounts, illegal drugs, counterfeit banknotes, engage in human trafficking, and many others.
Ransomware as a service (RaaS) is actually a thing on the dark web. Hackers get to offer their services in the form of ‘products’ which can be purchased by just about any interested buyers. This ransomware can then be used to infiltrate and take over devices, with the owners required to pay to have them unlocked.
But the dark web isn’t all about illicit or illegal content. There is also benign content like Blackbook, for example, a social network that is regarded as the Facebook of the dark web. You can find a ton of communities on the dark web centered around shared values like books, cryptocurrency, or internet freedom and anonymity.
Threats Lurking on the Dark Web
Takedowns of criminal websites and organizations happen quite often on the dark web. These takedowns are sometimes high profile, like the Silk Road, and may require collaborations between law enforcement agencies in multiple countries.
In spite of this, the dark web is still largely a wild and untamed place. More and more private servers get set regularly, and the market for illegal content continues to grow steadily. And that is why you must be careful if you decide to explore the dark web.
These are some of the threats that continue to lurk in the dark web which must be taken into consideration:
1. Scammers and Hackers
The dark web is home to scammers and hackers who employ all sorts of tricks to exploit their victims and steal their data. The data, which is made up of sensitive information, can be used to fleece their unwitting victims of large sums of money.
Scams come in several forms. Because the dark web is largely a market place, a scam may simply be refusing to carry out tasks after a financial transaction has already taken place. Because many of the transactions here are criminal in nature in the first place, there is not much in the way of seeking recompense.
How do you report to the police that the assassin you paid to murder someone has decided to run off with the advance?
There are various ways your location can be tracked on the dark web by hackers and scammers. Needless to say, this is not something you want happening.
2. Malware
Malware is already prevalent in the surface web. Just imagine how ubiquitous it must be in the dark web. Dark web users are always at a risk of becoming targeted with malware. The numerous market places in the dark web form excellent points of gathering for developers and buyers of malware.
Without taking adequate security precautions, you may just be the target for these nasty actors, who will seek to use their tools to infiltrate your device, leading to disastrous consequences.
Ransomware, phishing software, Trojans, and keyloggers are some of the risks you may be exposed to. A botnet is a network of devices like servers, computers, and phones that have been infected by a common malware. These devices can then be controlled by the threat actors responsible for infecting them, sometimes with the users unaware.
3. Monitoring by Law Enforcement Agencies
As mentioned earlier, takedowns of sites on the dark web occur all the time. Even if you are entirely innocent of committing (or attempting to commit) a crime, there is a chance that you can get into the cross-hairs of government agencies just for accessing a site of interest.
Trust me, you don’t want to get on a Government watchlist. But that is what happens to suspected patrons on criminal dark web pages, at least. To mitigate the chances of this ever happening, it is important that you stay away from known criminal marketplaces and pages. Also, you must take the right precautions to ensure your anonymity while on the dark web.
How to Access the Dark Web
As I earlier stated, the dark web and indeed the deep web as a whole cannot be accessed via a regular search engine or browser the same way you access web pages on the surface web.
If you want to visit a Facebook page on the surface web, all you need to do is type in the URL in any browser, like Chrome or Firefox. Alternatively, you can simply type in ‘Facebook’ in a search engine, and the website will be indexed. On the dark web, this will not fly.
To visit dark web sites, you have to go through an anonymized proxy network. Enter Tor. Tor is an acronym for The Onion Router. It is an encrypted and hence anonymous network that helps you browse the deep web – and the surface web too, actually. When you browse with the Tor browser, your data is sent through a series of nodes or relays, building up layers (onion, eh) of encryption.
The Tor browser is free and open-source. It is available for all the major operating systems – Windows, macOS, Linux, Android, and iOS.
So now we know what Tor is, let’s explore the process of accessing the dark web with it.
1. Install a VPN
The dark web has a sinister reputation, and while that can get exaggerated some of the time, it can actually be understated at other times. Exploring the dark web without a VPN is like running into a battle without armor – you’re leaving yourself open to get really hurt. And this is in spite of the level of anonymity the Tor browser offers.
To ensure your safety while browsing on the dark web, subscribe to a quality, premium VPN. The VPN you choose should come with relevant features such as a strict no-logs policy. This will guarantee that your activity is not stored on the VPN’s servers.
Your VPN must also come with leak protection for cases of connection interruptions. A kill switch automatically blocks your traffic when your connection is down to prevent your data from getting exposed to snooping eyes. DNS and IP leak protection are also essential.
Later on in the post, I will drop a line-up of my recommended VPNs to access the darknet, to protect your privacy.
2. Install and Activate an Anti-Virus
A VPN will grant you shield your data from interested parties, keeping you invisible to them. But invisible though you may be, you can still fall victim to malware. VPNs can do little to protect your device directly from malware like Trojans, spyware, ransomware, and more, all of which crawl the dark web.
For that level of protection, you should have anti-virus software installed and activated on your device. VPNs and anti-virus software work together to keep you fully protected from all kinds of potential cyber threats. Making sure you have both before accessing the dark web is essential.
3. Install the Tor Browser
You can download the Tor browser from the official website here. After downloading, install it on your device.
If you use Windows, double-click the .exe file and pick a destination folder. You can install it on a USB stick.
On the Mac OS X, double-click the .dmg file and drag the containing file to another folder. Again, this can be a USB stick.
For Linux systems, unpack the .tar.xz file using this command:
tar –czvf tor-browser-linux64-[…]tar.xz
The Android Tor browser is called Orbot. It can be found in the Google Play Store. While there is no official Tor browser for iOS, the Tor Project recommends that iPhone users use the Onion browser instead.
After installing, start the browser and make sure that running of scripts is turned off.
4. Browse the Dark Web with .onion Websites
You’ll find that the Tor browser does not look much different than any other browser at first. It is based on Mozilla’s Firefox browser, in fact. DuckDuckGo is the default search engine on the Tor browser.
While search returns are not indexed the way they on surface web browsers, you can still search to some extent. Because DuckDuckGo also works on the surface web, searching for content the regular way will bring back surface web pages. And that is why your searches should be streamlined to .onion sites.
Apart from DuckDuckGo, there are other helpful channels into the dark web such as The Hidden Wiki, Deep Web Links, Not Evil, Torch, and WWW Virtual Library.
The Tor browser and your VPN will work together to protect your privacy. But what method should you use for this combination? Should you connect to your VPN first, and then Tor (Tor over VPN), or do you go through the Tor browse first before connecting to a VPN (VPN over Tor)?
Tor Over VPN
This is the most popular way of accessing the dark web using both a VPN and the Tor browser. It is also the safest method. What it involves is simply connecting to your VPN’s service first before executing the Tor browser.
When you use Tor over VPN, you connect to a VPN server and your data is encrypted. Your IP address is also hidden. Tor over VPN adds several Tor relays between the VPN server and the final destination of the request. It extends the intermediaries between the VPN server and the device you are connecting with to the dark web.
A major advantage of this method is that even if the Tor network is compromised, your IP address will remain hidden and safe. It is useful for situations where ISPs block Tor Networks as the ISP will be oblivious to your Tor use due to the VPN’s encryption.
VPN over Tor
The alternative is using a VPN over Tor. This method is not considered as safe as Tor over VPN, but it does have its applications. The process is essentially the opposite of Tor over VPN.
Here, your traffic goes through the Tor network first, before reaching the VPN’s server. It is applicable for situations where you want to access websites that block Tor access. Your ISP is able to see that you are using Tor, unlike with Tor over VPN, but the websites you visit remain oblivious.
The fact that your ISP can see that you are on a Tor network is itself a disadvantage of using this method. The Tor entry node will also be able to see your IP address, which is not great for your privacy. Additionally, it is quite complex to set up.
The Best VPNs to Access the Dark Web
The dark web is a dangerous portion of the internet. The VPN you use for accessing it must come with certain features that will guarantee your privacy and security. It must also offer high speeds because the Tor browser naturally slows down your internet speed significantly.
1. NordVPN
NordVPN is based in Panama. It ranks top on most overall VPN lists and replicates that on this list. An immensely popular VPN, it comes with a ton of privacy and security features that make it ideal for visiting the dark web.
For instance, it comes with a unique Onion over VPN feature. This feature helps to create a smooth connection between your VPN and the Tor network. It provides an extra layer of protection than you would get using a regular VPN, keeping you completely anonymous to any potential bad actors.
NordVPN takes your security pretty seriously. It uses military-grade AES 245-bit encryption to scramble your data and render it intelligible to any interceptors. There are a variety of protocols to choose from, including OpenVPN and IKEv2/IPSec.
There is a very strict no-logs policy. No user or connection logs are saved on NordVPN’s servers, and so your internet activity cannot be linked back to you. NordVPN also offers a kill switch, so there is a scant chance that your data will become exposed in the case of downtimes.
A VPN with speed is essential for browsing the dark web. NordVPN comes with a huge network of 5,500+ servers spread across about 60 countries. Its servers are blazing-fast and very reliable. There are no bandwidth or data caps, so you will not ever get your speed throttled.
NordVPN is compatible with Windows, macOS, iOS, Linux, and Android. It permits customers to connect to up to 6 devices simultaneously on the same account. To try it out absolutely risk-free, you can take advantage of its 30-day money-back guarantee.
2. ExpressVPN
ExpressVPN is also an industry leader and a very popular VPN. It earns its reputation due to the priority it places on lightning-fast connection speeds and privacy protection.
Headquartered in the British Virgin Islands, NordVPN is out of reach of the jurisdiction of the 5/9/14 Alliance. As a result, there is a scant chance that your connection data and history will get handed over to authorities if they are demanded.
Even if it would, it couldn’t. ExpressVPN has a strict zero-logs policy that has been independently audited by PwC. It does not collect or store any sensitive information such as internet history, IP addresses, traffic destination, or metadata. Its servers run on RAM, not hard drives, so all the information on them gets wiped every time they are powered off.
In addition, ExpressVPN employs bank-level 256-bit encryption to protect your traffic. Available protocols include OpenVPN, its proprietary Lightway protocol, L2TP/IPSec, SSTP, and PPTP. It comes with an automatic kill switch and DNS leak protection.
ExpressVPN has over 3000 servers with a very wide reach spanning to 94 different countries. Its servers are reliable and extremely fast. In fact, ExpressVPN is consistently the fastest VPN service out of the several dozen that we test for speed. This means that it is ideal for combining with the Tor browser to ensure that your browsing does not take place at snail speed.
You can use ExpressVPN on all of the major platforms. It permits up to 5 connections at the same time on a single subscription. You can test its service risk-free, as there is a 30-day money-back guarantee when you subscribe.
3. CyberGhost
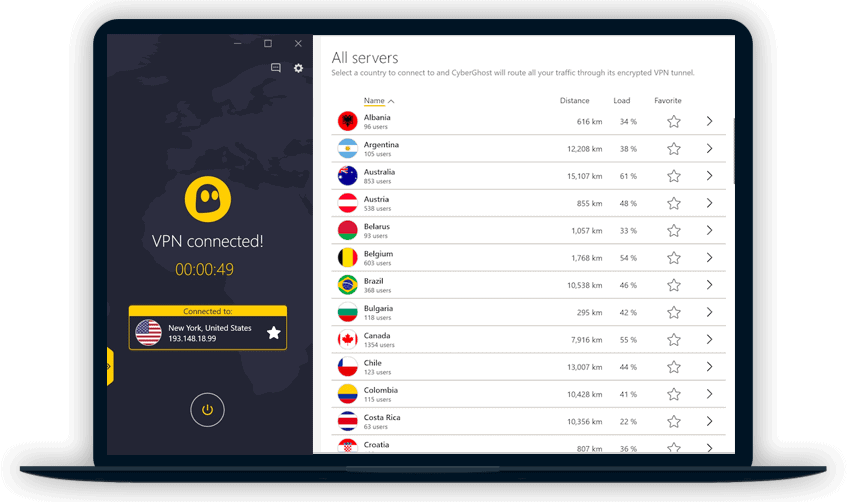
Finally, we have CyberGhost, and you will find that it is a perfect blend of pocket-friendly pricing and top-notch security. It is based in Romania, which is great, as the country does not fall under the 5/9/14 Eyes Alliance jurisdiction.
CyberGhost does not keep logs. It does not store any information on its servers that may be used to implicate you in the future or track down your location. This includes your IP address, DNS requests, metadata, or history.
For maximum security for browsing the dark web, CyberGhost offers a NoSpy feature. It comes in quite handy if you want to hide your usage of Tor from your ISP. The servers that operate this feature are based in CyberGhost’s private data center, and so away from the risks of attacks. CyberGhost offers this service as an extra paid feature.
What’s more, your traffic is protected by the AES 256-bit encryption, which is the industry standard. It comes with OpenVPN, WireGuard, IKEv2, and L2TP/IPSec Protocols. There is a kill switch to protect you from the risk of leaks.
CyberGhost has a very huge network of over 6,700 servers spanning 90+ countries. Impressively, more than 1,100 of those servers are spread across the United States. While CyberGhost may not be as fast as NordVPN or ExpressVPN, you will find that its servers are generally speedy and reliable.
CyberGhost is compatible with Windows, macOS, iOS, and Android. It allows you to connect up to 7 devices simultaneously on one subscription. CyberGhost’s money-back policy is very generous. If you decide you are unimpressed with the service, you can ask for a refund within 45 days and get your fee back, no questions asked.
FAQs
1. Is the dark web legal?
The dark web is a hotbed for crime and criminals. There are all sorts of nasty actors in there, with tons of market places for illegal and illicit activity.
But that does not mean that the dark web is all bad, or illegal for that matter. There are perfectly legal transactions carried out on the dark web every day together with communities built around harmless activities. It is also used by law enforcement agencies for monitoring the activities of criminal entities.
2. Is Tor legal?
Some ISPs may throttle or block Tor traffic because of the illegal activities carried out using the Tor browser.
However, Tor and the Tor browser are completely legal. You will not be breaking any sort of laws by using Tor, as long as you do not initiate or partake in any illicit or illegal activities.
3. Is visiting dark web pages with illegal activities a crime?
Well, not in itself. But it certainly is a gray area. There are lots of pages on the dark web with completely innocuous activity and content. Generally, you will not run afoul of the law if you explore those onion websites.
Simply visiting dark web pages that are marketplaces or centers for illegal activities is another matter entirely. Although it is not a crime in itself in many countries, you would potentially be opening yourself up to intense scrutiny if you are detected. The sensible decision would be to stay away completely.
4. How can I protect my data in the dark web?
You must take adequate precautions every time you access the dark web. It is proliferated with hackers and scammers, malware, and government monitoring. Simply clicking a bad link can lead you down a rabbit hole that you may find very difficult to climb out of.
For complete anonymity and security, you need to combine the protection offered by the Tor browser, anti-virus software, and a top, premium VPN. I recommend NordVPN.
Summary
With millions and millions of web pages, the internet may seem like a very huge ‘place’. It is, and that’s only what we can interact with using traditional systems. Underneath the surface, there is a much larger portion of the web which is decentralized. The dark web is a subset of this.
To access the dark web, you should make sure that you do not leave your device and data exposed to the threats that swarm in it.